I woke up at 5am on the day we were to go to Uppsala to meet Annie, who was going to read some of Sam’s poetry at an evening performance at the English Bookshop, during Uppsala’s yearly Culture Night. Annie had asked me to say something about collaborating with Sam on a book of poems and photographs that we had published near the end of his life.
I awoke with thoughts going around my head of what I would say, and decided to get up and write them down, as I’d either not get back to sleep if I didn’t, or remember them if I did. So in the apartment that we had spent such memorable times, I wrote as swiftly as I could.
*****
I always looked up to Sam – as a young boy, in a physical sense – he was a towering figure dressed in Levis’ 501s, Bass loafers with cream socks, a light blue shirt, with a v-neck dark blue pullover, a canvas-coloured London Fog raincoat.
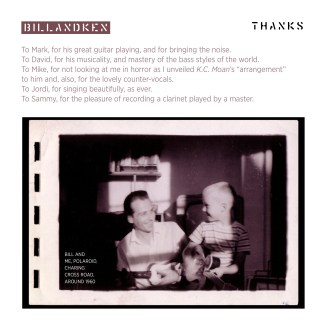
As a teenager, it was less Sam’s physical presence as much as his intellectual one – it was about the expanding of horizons. I can see him now, padding around my parents’ Charing Cross Road flat, a suitcase full of books and notes and records – always open – that spoke of exotic places, exotic thoughts, exotic music.
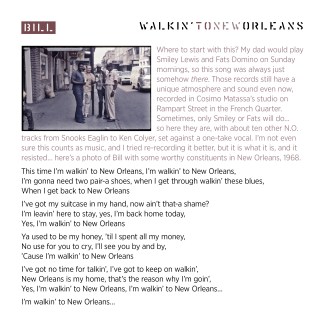
In 1968, we were sent three plane tickets – Pan Am, London to New York – to visit with the Charters. So for three weeks we soaked up America with Ann and Sam as our guides. My dad Bill was sent on his first visit to New Orleans, to hang out in the places – and with the people – that his brother Ken had written about so vividly in 1952 when he jumped ship to play with his heroes. We, meanwhile, headed to the Newport Folk Festival to stay in a spookily empty school dormitory and watch Arlo Guthrie and Janis Joplin and Buddy Guy and Junior Wells. Sam was Buddy and Junior’s record producer, and he took me backstage to their trailer where Buddy let me hold his guitar. That was an education right there.
*****
When Sam came through London in 1970, en route to a new life in Sweden (he’d felt that staying in the States at that point would mean joining the Weathermen), he left with me some of his favourite albums. There was God Bless Tiny Tim; there was I-Feel-Like-I’m-Fixin’-to-Die by Country Joe and the Fish (produced by Sam); more indelibly, Music From Big Pink was there, and I remember Sam saying that Richard Manuel’s “In a Station” was his favourite track.
Around this time (I was about fifteen) there was an open invitation to visit whatever project Sam was currently working on, so after school most days and weeks that he was in town, I would make my way over to Sound Techniques, a recording studio housed in an old dairy building off the King’s Road in Chelsea. I’d sit on the couch at the back of the control room as Sam produced American protest singers, English folksters, blues guitarists and Ragtime Orchestras, always with the same good humour, but also with an intense desire to bring out the core of whichever artist he was working with.
I saw his rapport with them, his subtle direction of them, and his real love for what they did. I experienced at first hand the camaraderie of musicians, the application of their gifts, their ability to come together and coax magic from thin air. These things have always stayed with me.
*****
Sam had a really sophisticated knowledge of music and its history and such a wide-ranging love of song. He’d gone with Ann on voyages of discovery that, for some, equaled Stanley’s trek to find Livingstone or Vespucci, America – voyages that took them back into the struggles and art of an earlier America. Yet he wore his knowledge lightly and often worked with music rooted in apparent simplicity, always coming back – in some way – to the blues, a music that had spoken across states and racial boundaries and decades of time to him. And although he often wrote of the past, it was always the future for Sam: there was the next project, just around the bend, to find and illuminate another neglected or wrongly understood strand of music. It’s no coincidence that one of his final journeys was to tell the little-known story behind the creation of the songbook Slave Songs of the United States, and the woman who made it happen, Lucy McKim Garrison.
When I was eighteen, about to go to art school, Sam was in town, working. He had the record company, who he’d just written a liner note for, make the cheque for his payment of £60 out to me. A week before, I had seen an advert for a Leitz enlarger, a photographic printer that allowed you to turn a bathroom into a darkroom. With Sam’s cheque I bought it and began my practical journey into photography. I didn’t become a photographer – music and design were what I became mixed up in – but it gave me an appreciation of the commitment photographers, like musicians, need to make their work happen.
*****
Sam and Annie have been a constant and wonderful presence in the life of my family and 14 months ago, when Sam asked if a package had arrived in London ahead of our trip to Stockholm, I had no idea that he was asking me to collaborate on a project with him, designing and adding photos to a collection of his London poems. I was touched and thrilled to do it, worried about my rusty photographic skills, but up for the challenge. I remembered the day in 1973 when we trekked around the city finding poems in boxes at the locations that had inspired them, before meeting up with Sam in a pub in Hampstead where he put a cover on our sheets and stapled them together into a book. Batting the design of the new book, back and forth across the internet, was among the best experiences of my working life…
And when I think of Sam now, as I often do, I mostly think of him laughing, as he talked of the absurdities of life, of the footwork of Zlatan Ibrahimović, of finding rare sheet music in the Canary Islands, of the value and import of friendship, love and art. He taught me to pay it forward; to work with collaborators that you liked; to encourage other people’s talent. He was an inspiration to me, as he was to many others, and he showed me not only how to be enthusiastic but – more importantly – how best to use that enthusiasm.
Here’s “Must be Some Way to Repay You”, a song that I wrote for Sam using words from various sources edited together: Richard Manuel’s “In a Station”, Country Joe’s “Here I Go Again” and Elmore James’ “The Sky is Crying”.